SOC250 — APT35 HyperScrape Data Exfiltration Tool Detected (LetsDefend)
Originally published on Medium: https://medium.com/@brandonlove2150/soc250-apt35-hyperscrape-data-exfiltration-tool-detected-letsdefend-f85d6388111f?source=rss-024d132ba4b7——2
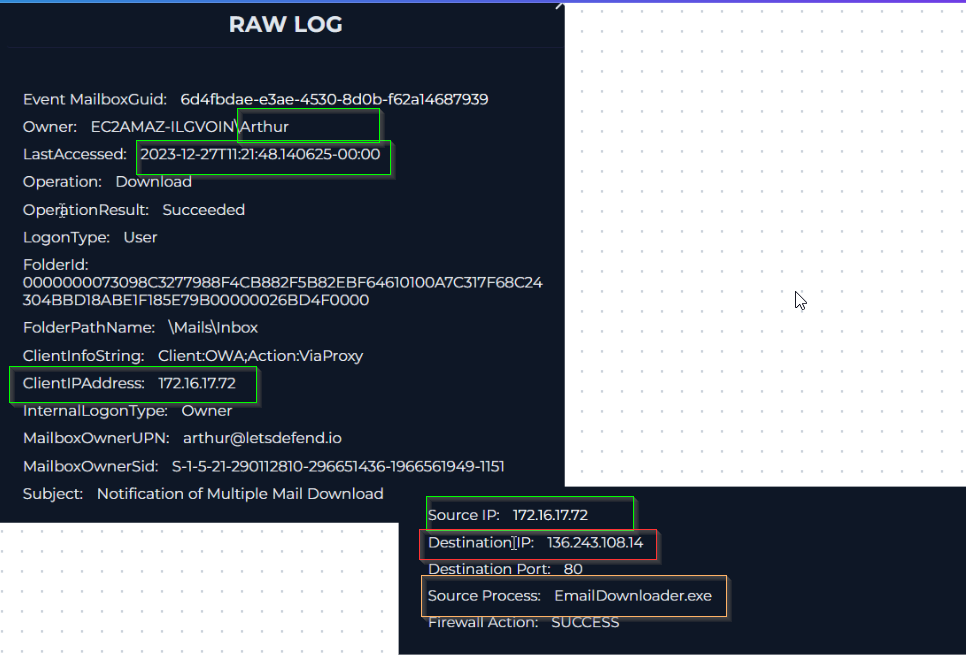
SOC250 — APT35 HyperScrape Data Exfiltration Tool Detected (LetsDefend) I just completed another SOC Alert from LetsDefend, and this alert was for HyperScrape Data Ecfiltration Tool Detected.
SOC250 — APT35 HyperScrape Data Exfiltration Tool Detected (LetsDefend)
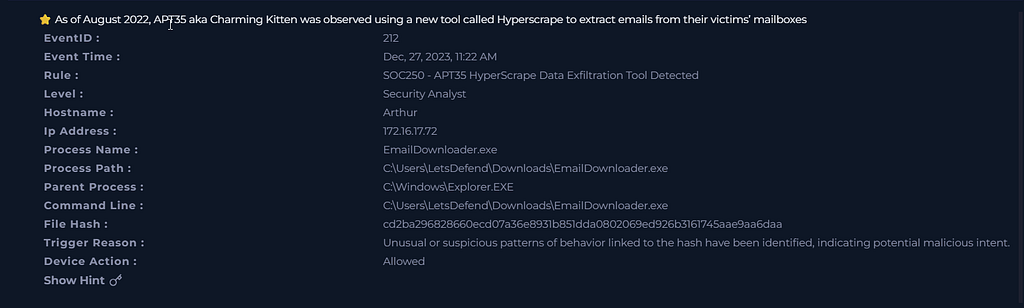
I just completed another SOC Alert from LetsDefend, and this alert was for HyperScrape Data Ecfiltration Tool Detected. This alert provided another opportunity to gain hands-on experience in responding to an alert, completing another playbook, and analyzing logs.
SOC Alert
WalkThrough
Start of Playbook
After starting the playbook, I first searched the MD5SUM Hash cd2ba296828660ecd07a36e8931b851dda0802069ed926b3161745aae9aa6daa. This hash was flagged as malicious, scoring 51 on VirusTotal.

VirusTotal
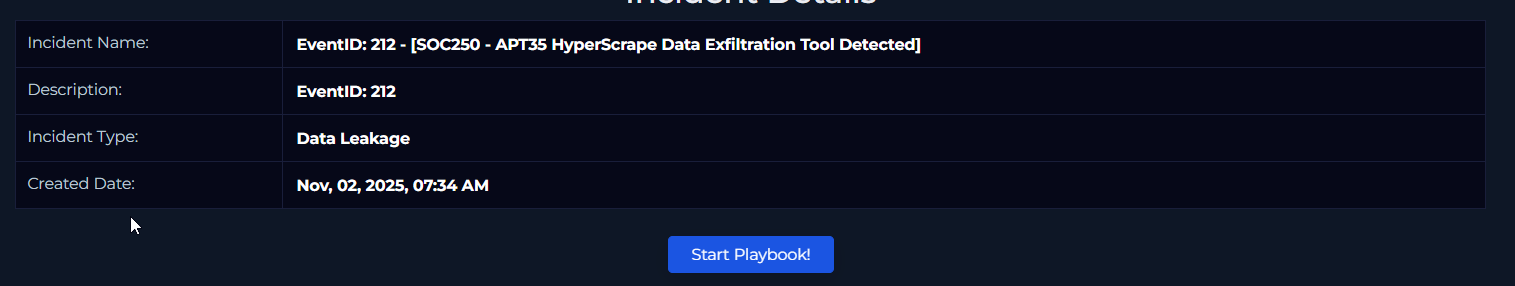
We can see that ALYac lists it as a Trojan Email Downloader. Examining the history section of the file reveals additional information about it.
History
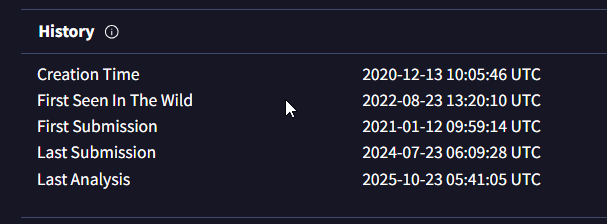
The first log I searched was the log management section on the GUI of LetsDefend. From this log, we can see that at 11:21:48, a file was downloaded using a process called EmailDownloader.exe, which was downloaded from 136.243.108.14. We can confirm that the host was Arthur and the IP address is 172.16.17.72.
Log Management
Since we have seen that the process EmailDownloader.exe was run, the next step is to check the emails of arthur@letsdefend.io. After checking the emails, there was no traffic. This makes the alert more suspicious; further investigation into the endpoint, Arthur, is needed.

Endpoint Logs
Two logs were captured around the time of the alert. The first instance occurred at 11:21:37, when the explorer.exe process triggered the emaildownloader.exe process to download the suspicious file. The second process was MpCmdRun.exe, which ran the command SignaturesUpdateService with the -ScheduleJob and -UnmanagedUpdate parameters. This means that the file was able to modify the signatures.
Using all the information that was gathered, these were my answers to the questions in the playbook.
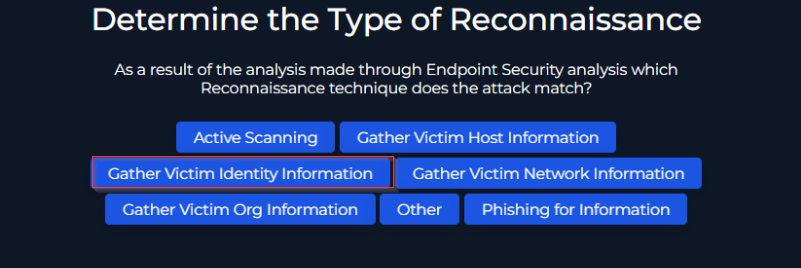
Question 1
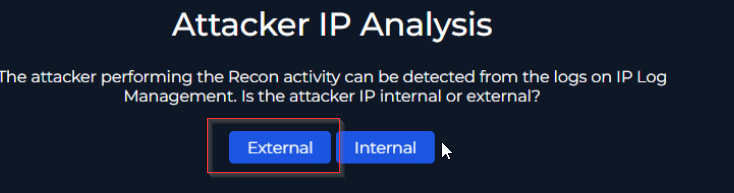
Question 2

Question 3

Question 4

Question 5
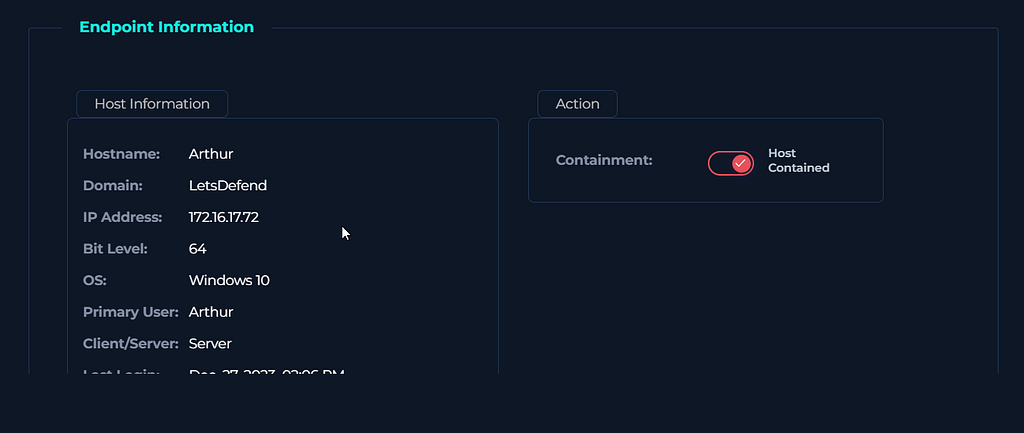
Containment

Completion
Analyst Notes
On December 27, 2023, at 11:22 AM, an alert was triggered for Unusual or suspicious behavior linked to a file (cd2ba296828660ecd07a36e8931b851dda0802069ed926b3161745aae9aa6daa).
After reviewing the hash file, it is identified as malicious by VirusTotal, with a score of 51.
This file ran an EmailDownloader.exe process; however, upon analyzing the email security, no emails were found to be linked to the host machine or its email address.
Analyzing the logs, we can see that a file was downloaded at 11:21:48. Examining the Host endpoint (Arthur) in the network logs reveals that several processes were run.
The first one that triggered the email download was at 11:21:37, and it ran explorer.exe to download the file with EmailDownloader.exe.
The second process, run at 11:38:10, was MpCmdRun.exe, which executed the command “SignaturesUpdateService -ScheduleJob -UnmanagedUpdate”.
The host was contained, and no other endpoints were compromised.
I suggest blocking the attacker’s IP address and resetting the host’s password.